Approximately 8 out of 10 people have clicked a link in an email without second thought. This number is also guilty of using the same password for like five different accounts.
You are probably a part of this statistic, and you do not understand the effect of your actions.
The risks that come with being a part of the digital world increase daily, and a problem that used to be seen as a challenge for big companies is now at your doorstep.
Cybersecurity awareness is no longer just a buzzword that IT departments throw around. It is now one of the most important pieces of knowledge you must gain in your life.
So whether you own a business, work under someone else, or spend most of your time on the internet, you need to know how to protect yourself from cyber threats.
Let’s dive in.
Key Takeaways
- Understanding cybersecurity helps you spot threats before they cause damage
- The biggest tricks attackers use are phishing, malware, and social engineering
- The way to protect yourself is by using strong passwords and a secure network
What Is Cybersecurity Awareness
Cybersecurity Awareness refers to the act of educating an individual or other individuals on the possible dangers of the internet.
It is also about being aware of how to avoid cyber threats and the manner in which one should act in case security is compromised.
It can be considered as being digitally street smart. This means gathering the knowledge that enables you to navigate the internet without getting burned.
Never Worry About AI Detecting Your Texts Again. Undetectable AI Can Help You:
- Make your AI assisted writing appear human-like.
- Bypass all major AI detection tools with just one click.
- Use AI safely and confidently in school and work.
So, just like how you would not leave the doors to your apartment open, cybersecurity awareness is about not leaving the ‘digital doors’ of your professional and personal life open to damaging threats.
To put it simply, cybersecurity means having knowledge of the security threats and how to prevent possible risks. It helps you know the steps to take before something goes wrong. You can actually say that it is all about being prepared and not paranoid.
You must understand that the concept of being aware of cybersecurity is not just for you alone. Cybersecurity awareness training has become a priority for organizations because the unconscious actions of one employee can cost the company millions.
Sadly, incidents where an employee clicks the wrong link happen very often.
In summary, cybersecurity awareness means knowing:
- What online threats are
- How attackers can trick you
- What to do to protect yourself
That is why we have National Cybersecurity Awareness Month. It helps to remind people and companies that it is their duty to be safe on the internet.
Cybersecurity Awareness
So, in your quest to know more about cybersecurity awareness, what are the threats you need to be aware of? The following are the major scams you need to know:
Phishing Emails and Fake Links
Phishing is the most commonly used mode of hacking in cybercrime. It is an approach where personal data, such as usernames, passwords, and credit card details are obtained through fraudulent emails, websites, texts, and links.
The FBI Internet Crime Complaint Center (IC3) states that phishing constituted the largest cybercrime in 2021, with about 323,972 victims reported in 2021, and more than 44 million dollars lost. The reason why this trick keeps working is that it keeps evolving.
It is as simple as you getting an email that looks like it was sent by your bank or your boss, saying that your account has been compromised. You click that link, and it’s a clean sweep; all you have is gone.
These days, phishing emails are beginning to look oddly legitimate. Scammers have creative means through which they replicate logos, find methods of imitating the style of writing, and come up with email addresses that are almost similar, so they can appear genuine.
You can get an email that says, “Your account has been suspended. Click here immediately.”
One thing you will observe is the urgency given in the message, and that is typical of phishing. It makes you believe that you have something to lose when you fail to take a particular step.
This is the reason why whenever you receive an email or send an email to someone, you must pause and scan to see any form of interference.
You can hover on the link to discover where it would bring you, and in case something does not add up, go to the official site.
The red flags to be observed include:
- Weird email addresses
- Messages with a sense of urgency
- Suspicious links that do not match the official website
- Bad grammar
Malware and Ransomware Attacks
Malware is a software created to gain unauthorized access and cause damage to your system.
While ransomware is the worst version of malware, it gets into your system, locks you out of your computer, and asks for payment to gain access back.
Hospitals, schools, businesses, and rich individuals who have something to lose are the common victims of malware and ransomware attacks.
It is estimated that approximately 300,000 new malware are developed each day. Another way they get in is via email attachments, fake software downloads, or questionable websites.
The most effective way of preventing these attacks is to keep your software up to date and to ensure that you have a good antivirus program.
In addition, you can also make sure that you watch what you download, and when a download feels suspicious, do not open it mindlessly.
Social Engineering Attempts
Social engineering is when someone manipulates you into giving up confidential information by pretending to be someone you know and trust. This method requires more psychological effort than technical.
Scammers only need to hack your trust as they make you believe that they are your coworker or family member, so they do not even need to hack your computer.
They might:
- Pretend to be your CEO, asking for sensitive information
- Call posing as tech support
- Sending you a message pretending to be someone you know
Apart from pretending to be someone else, another social engineering attempt is powered by the bandwagon effect. The bandwagon effect leads us to conform to the behaviour of other people.
The chance that you would become a victim of a phishing scam is high because you clicked on a link that someone you know clicked on too.
Individuals who engage in social engineering frauds use fear, urgency, and power. So the next time someone calls you and urges you to do something right now, the best thing is to take your time and verify.
You are supposed to seek to establish the identity of someone using another channel before providing information. A quick phone call can save you from trouble.
Safe Password And Account Practices
One of the aspects of keeping your account secure against cybercrime is the use of a strong password. Putting your password as password1234 or the name of your pet makes you an easy target for hackers.
To keep your passwords and accounts safe, you should be doing the following:
- Make Use of a Password Manager: A password manager helps you generate strong and unique passwords for all your accounts. It also helps to securely store passwords, just in case you cannot remember all of them. You are supposed to conduct your research and locate the password manager that best fits.
- Never Use the Same Password for Everything: You must have different passwords so that if one account gets compromised, it doesn’t affect the others.
- Turn on Two-Factor Authentication: It is always important to ensure that there is a second level of authentication on your account. This means, even when someone hacks into your password, he/she will not enter it without undergoing the process of another verification.
- Change Your Passwords Regularly: To secure yourself, change your passwords at intervals. This may sound stressful, but it is important, especially for accounts that hold sensitive information. You can see it as one of the simplest ways to stay protected.
Protecting Devices And Networks Effectively
One of the largest components of your online security is your devices and networks, and here is how to ensure that they are safe:
- Install the Latest Software Update: Software updates are not only concerned with obtaining new features. It is one means to fix security vulnerabilities that are exploited by hackers. Before you cancel or delay that update, consider the benefits you could be receiving.
- Use VPN: VPN is very important especially when you are using a public Wi-Fi. Connecting your device to a public Wi-Fi might seem like an innocent action but it is one of the fastest ways of losing your information. With VPN, you will be able to encrypt your connection, that is, even if someone tries to monitor what you are doing, they won’t be able to access your information.
- Install Firewall and Antivirus Software: A good firewall and Antivirus software give you a better chance to defend your devices. Therefore, you should make sure that it is always on and updated.
- Be Careful of what you Plug into your Device: USB drives not bought by you can corrupt your device and leave it vulnerable to malware. Avoid using drives if you are not sure of what you are using.
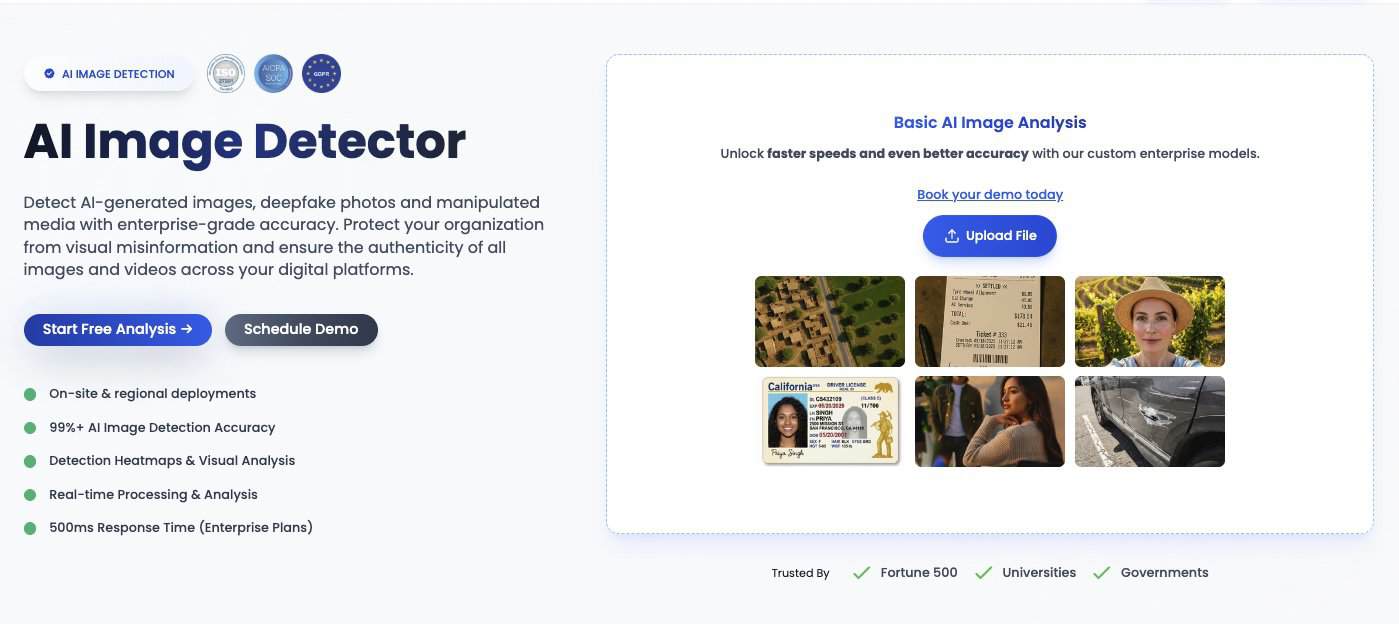
Aside from using all these tips, you can also resort to the Undetectable AI’s AI Image Detector. It ensures that images have not been manipulated.
So, if an image looks strange, your best bet is to scan it with the Undetectable AI Image Detector.
Recognizing Deepfake And Manipulated Content
Now, this is where things get a bit more futuristic but very real. Deepfakes are artificial intelligence-generated videos, pictures, or audio that appear and sound very realistic.
Most fraudsters utilize it as a means of convincing others, relaying false information, and making people make poor choices.
This may sound unbelievable and scary, but with the right knowledge, you can prevent yourself from falling for deepfake scams and manipulated content.
Identify Fake Videos and Audio
Deepfake technology is growing better each day; however, that does not imply that it does not commit errors. One simply has to be aware of what to be wary of.
That is, the obvious red flags that are common with fake videos and audio.
When looking at any video, watch out for:
- Slight lip-sync mismatches
- Unnatural blinking
- Strange tones in voices
- Odd lighting inconsistencies
- Out of character behavior for the person in the video
- Weird lighting
Basically, if something feels slightly off, trust your instinct.
Check Sources Before Trusting Content
It is very important that before you share or take action on any piece of media, you need to ask yourself, “Where did this come from?” “Is this verified?
Those two minutes of fact checking can save you from misinformation and scams.
Anytime you get a video you are not certain about:
- Check the source
- Look for official announcements
- Cross-reference with trusted news outlets
- Don’t let viral panic override logic
Educate Team Members About Risks
As a manager or a team lead, you must ensure that you provide cybersecurity awareness training for employees on a regular basis. It can be used to make sure that your team becomes accustomed to new technologies such as deepfakes.
Having a team that can’t spot a manipulated video is vulnerable to your organization. So regular training, no matter how short, can make a real difference.
There are artificial intelligence tools that prevent you from relying on human eye detection alone. One of these tools is the TruthScan Deepfake Detection.
It helps you spot fake videos or audio sent by scammers. With this tool, you are not just relying on your own eyes to detect deepfakes media.
Boosting Awareness With Undetectable AI
Technology is not only a problem but also a solution. AI tools can be deployed to your advantage in the case of cybersecurity. One of the top providers of these tools is Undetectable AI.
Undetectable AI has tools that can help you verify the authenticity of any media.
You can use the Undetectable AI’s AI Humanizer to make AI-generated safety tutorials, and alerts sound natural and easy to follow. That way, employees can actually read and understand them easily.
When warnings and training materials actually sound human and approachable, people pay attention and retain the information better.
TruthScan also helps to verify links, emails, and documents for authenticity. With this tool, there is no need to play a guessing game about whether an email is legitimate or an image is safe to download.
TruthScan does the heavy lifting so you can make informed decisions.
A combination of these tools and the continuous cybersecurity awareness training for employees will allow building a proactive defense mechanism rather than a damage control mechanism.
Find out how our AI Detector and Humanizer work in the widget below!
Final Thoughts
Criminals become increasingly intelligent, and scams are becoming more authentic with the development of artificial intelligence.
It is in this regard that you should invest in cybersecurity awareness to make sure that you have the appropriate knowledge.
As we move into cybersecurity awareness month 2025, cease to think of cybersecurity as a corporate campaign and more of a wake-up call to be aware and ensure you check before you leap.
Verify suspicious content and stay one step ahead of AI-powered scams with Undetectable AI.